The Digital Underground and Dark Web – A Treasure Trove of Actionable Intelligence
March 17th, 2021

The Dark Web is home to many of the fraudsters and cybercriminals targeting financial institutions. It provides a safe haven for criminal activity, a platform for storing and exchanging compromised data, and a means of communication and collaboration. But this activity extends far beyond the Dark Web. In recent years, cybercriminals have gradually shifted operations to other platforms to evade law enforcement agencies tracking the Dark Web. Here at Q6 Cyber, we refer to the universe of these platforms as the “Digital Underground”, encompassing not only the Deep and Dark Web, but also encrypted peer-to-peer messaging applications such as Telegram and Discord, malware networks and botnets, and other technical infrastructure.
Financial Crimes in the Digital Underground
The Digital Underground facilitates a wide range of financial crimes globally. For example:
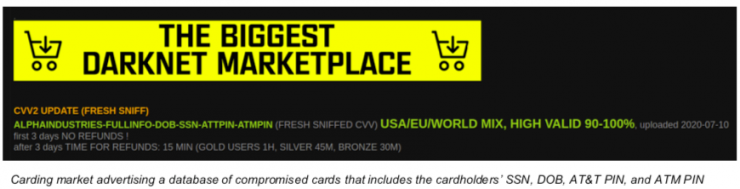
- Stolen financial account data is sold à la carte or via large troves on ‘black market’ e-commerce sites;
- Huge volumes of compromised payment card data are traded;
- Financial mules are recruited and shared;
- Stolen PII or synthetic identities are offered;
- And tools to evade security and anti-fraud controls are shared.
Such data and tools are leveraged by threat actors carry out a variety of financial crimes and fraud schemes, including account takeovers, payment card fraud, stock manipulation, SBA and unemployment fraud, money laundering, or the creation of synthetic identities for the purpose of securing a fraudulent loan, among others. The data and activity in the Digital Underground is not limited to the largest financial institutions or specific regions; in fact, we regularly observe financial institutions of all types and sizes targeted – from leading banks and brokerage firms to regional and community banks and credit unions.
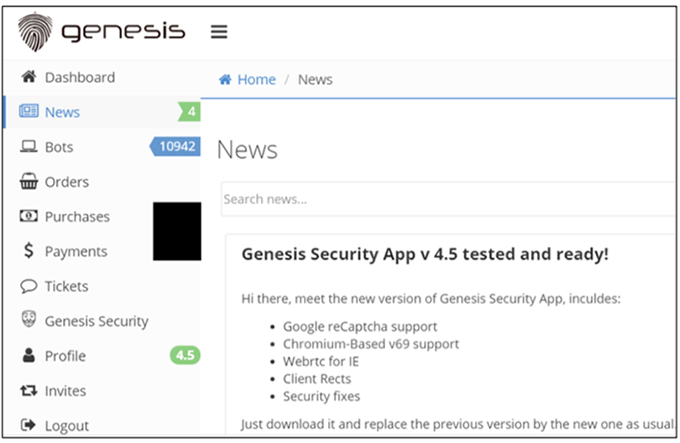
Homepage of Genesis, an underground marketplaces for compromised financial and other online accounts
COVID-19 Pandemic a Huge Tailwind
In recent years, the amount of data and activity across the Digital Underground has grown exponentially, driven by ever-growing data breaches and increasingly sophisticated cybercrime tools. Then came COVID-19. The pandemic has been a boon to cybercriminals and fraudsters. The rapid shift to digital banking and commerce provided ideal conditions for data theft and financial crimes, driving surges in account takeover scams, impersonation scams, and money mule schemes, to name just a few. The economic uncertainty and high unemployment rates further fueled financial crimes. During 2020, the FBI took action against 2,300 money mules, an increase of 383 percent over 2019.
To illustrate the trend, let’s focus on account takeover scams. Account takeover (ATO) is one of the most effective and common forms of fraud. Using credentials compromised through malware or other means, fraudsters can gain access to an existing account and ‘takeover’ said account for the purpose of siphoning funds through transfers or other transactions. In the Digital Underground, compromised account credentials are available for purchase at a relatively low cost. These credentials are typically acquired through malware campaigns, during which victims’ computers and other devices are infected and the financial account credentials and data are exfiltrated. The magnitude and sophistication of malware campaigns increased during the pandemic, and found more victims due to the exponential rise in online activity. All this led to a surge in ATO scams in 2020, increasing 650 percent in Q4.
Fighting Back
Without a doubt, the Digital Underground enables financial crimes and fraud at scale. As the troves of compromised data available on the Digital Underground continue to grow alongside criminal tools and services, financial institutions are finding themselves at the vanguard in the fight against more sophisticated adversaries. Being reactive against these threats means accepting losses, customer friction, and reputational damage.
However, the Digital Underground can also be a tool to fight the very same fraudsters and cybercriminals who frequent it. The best way to proactively disrupt these threat actors is to carefully monitor the Digital Underground and answer the following questions: Who is targeting my financial institution? What are their objectives? What are they planning? What corporate and customer data has been compromised? By using the Digital Underground as a valuable intelligence tool, instead of an ungovernable threat, institutions can intercede and preempt financial crimes and fraud. Consider the following real-world examples, taken from years of our experience.
Customer Account Takeover Campaign – A cybercriminal ring executed a sophisticated malware campaign targeting customers of a large global organization, netting hundreds of victims. The cybercriminal ring planned to access the victims’ bank accounts using remote desktop protocol and cash out through fraudulent wire, ACH, and Zelle transactions. Leveraging intelligence collected from the Digital Underground, we alerted the bank to many of the compromised victim accounts ahead of the cash-out, as well as actionable information regarding the operation and the cybercriminal ring. The bank took immediate steps to protect these customer accounts and track the activities of the threat actors, preventing a 7-figure loss event.
Payment Card Fraud – Monitoring a wide set of underground marketplaces and communities, we detected a large volume spike in compromised credit and debit cards of a financial institution. We shared the data with the financial institution, which proceeded to: 1) flag the compromised cards with heightened risk scores to mitigate the likely upcoming fraud wave, and 2) perform a common-point-of-purchase analysis to identify the source of the card data breach. The financial institution succeeded in identifying the source and notified the relevant parties, preventing a significant loss event and customer disruption.
Zelle Fraud –The adoption of Zelle over the past few years attracted financial criminals due to the instantaneous nature of the payments. Cybercriminals who recruit and manage networks of financial mules in North America offer these mules ‘as a service’ to other fraudsters and criminals on the Digital Underground, who use these mules for a range of financial crimes, increasingly leveraging the Zelle platform. Collecting intelligence on the Digital Underground, we identify mule accounts in the early stages of recruitment and provisioning. The intelligence is used by financial institutions to block Zelle and other transactions associated with such mules.
New Account Openings – No matter how much money is spent on implementing security controls, financial institutions can’t change the fact that their biggest vulnerability is the customer. Whether it’s through the creation of a synthetic identity using stolen PII or through malware, it’s more often customers that present the biggest blind spot. Understanding what compromised PII and financial account information is circulating in the Digital Underground is the best way to proactively protect against fraudulent new account applications, loan fraud, and other fraud types that leverage digital identities. Using intelligence collected from the Digital Underground, financial institutions could do more to add friction and enhance customer validation.
SBA and Unemployment Fraud – U.S. government assistance programs have attracted fraudsters and cybercriminals from around the world. The Digital Underground has been buzzing with such activity, including tutorials and guides, PII, tools, and more. Gaining insights into the latest tactics and synthetic or stolen personas utilized by such fraudsters has helped financial institutions disrupt these operations.
In summary, many financial institutions are incorporating E-Crime Intelligence – sourced from the Digital Underground – to identify and eliminate fraud and financial crimes before an attack is carried out. Successfully leveraging such intelligence is a powerful capability that transforms anti-fraud and financial crimes organizations from reactive to proactive.
Get in touch with Robert Villanueva, E-Crime Intelligence | U.S. Secret Service (Ret.), Q6 Cyber at rv@q6cyber.com.
For more information, watch the on-demand webinar on monitoring the “Digital Underground” here with Q6 Cyber.




